Does ISO 27001 Cover the Requirements of GDPR?
In today's ever–evolving digital environment, the protection of personal data has become more critical than ever. As data breaches occur with greater frequency, the cyber–security standards that were put into law 20 years ago are no longer enough to protect the information of businesses and customers that interact online. The larger the database, the graver the consequences of a breach for parties at both ends.
In the present technological landscape, a more advanced set of regulations has been needed to mitigate the dangerous and costly consequences that often come with online data collection. To that end, new regulations are set to take effect across Europe that will impact all businesses around the world that do business with residents of that region. As companies prepare to bring their systems into compliance, best–practice standards are becoming increasingly popular.
What Is the GDPR?


The General Data Protection Regulation (GDPR) was developed by the European Union over a four–year period to serve as a legislative solution to issues regarding data protection in the present day. Currently, laws regarding data protection in the United Kingdom are based on the Data Protection Act of 1998 — an update of the 1995 EU Data Protection Directive — which itself was designed to handle security issues as understood by lawmakers and programming experts in the years leading up to the millennium.
The GDPR is intended to solve security issues that have emerged over the past two decades since the development of cloud technology and its impact on data security. The new regulations, which go into effect in 2018, will impose strict fines throughout the EU for breaches in data security. The law will also offer more power to citizens in regards to what companies can do with private data. While the new law will be beneficial on all sides, the GDPR has ostensibly been designed to protect consumers.
What Is the Purpose Behind the GDPR?
There are two main reasons for the new protective regulations of the GDPR. First and foremost, the regulations are designed to protect customer data in the new digital environment. In an age where companies like Facebook and Google share the personal data of account holders in exchange for site access and features, the GDPR seeks to return more control of the situation back to the user. This could make EU users less wary of sharing information on such platforms, would, in turn, allow the companies behind such platforms to serve the European public better.
The current laws that are in place were drafted long before the current digital environment, in which cloud technology has made it easier than before to exploit private data. With the heightened restrictions imposed by the GDPR, the EU aims to renew the public's trust in the ever–developing digital arena. Fears of advanced online hackers could be reduced, if not eliminated, by the new regulations.

The other reason for the GDPR is to establish a clear–cut set of regulations under which businesses can operate in regards to the handling of customer data. With these new rules, the boundaries would be easier to understand on both the corporate and consumer end, which would make it easier for businesses to earn and hold the trust of customers.
With the laws on data protection more clearly defined throughout the EU, the GDPR could save the European business economy roughly €2.3 billion a year. That savings, in turn, could be passed onto consumers.
When Will the GDPR Go Into Effect?
The GDPR will go into effect across the EU on May 25, 2018. While the new law was agreed upon two years before the date as mentioned earlier, businesses have been given 24 months to bring their systems into compliance with GDPR regulations. For thousands of companies worldwide, the new law has led to widespread adoption of best–practice standards. 
Still, it remains to be seen just how immediate the new regulations will be implemented across the board. Despite the fact that most IT security professionals have acknowledged the scope of the GDPR, less than half of them have readied their systems for the new law. According to a recent Imperva survey of 170 security staff professional, only 43% have examined the probable effects of the GDPR and the standards it will set for corporate legal compliance in the realm of data privacy. A lot of organizations have yet to understand the effects of the new law.


Granted, many of the respondents in the Imperva survey were based in the US, but the impact of the GDPR will still be felt across the pond. More than a fourth (28%) of those surveyed said that they didn't understand how the GDPR would impact the way that American companies handle the data of European customers. Consequently, few of the stateside parties for whom the law concerns have taken steps to prepare for the implementation of the GDPR.
The trouble is, organizations in the US, Canada and other parts of the world that gather the data of EU residents will be subject to the same penalties as European companies that fail to comply with the new regulations.
Who Does the GDPR Effect?
The two parties in the realm of data security that are directly impacted by the implementation of the GDPR are the controllers and processors of digital information. The first of those parties, the controllers, are the entities that determine the methods and reasons for the processing of user data, while the latter side, the processors, are the entities that are responsible for the processing of user data. Together, the two parties are the balancing act behind personal data security on a global scale.
The controlling party would be represented by any organization — be it a company, a charity or a government entity — that handles user information. The processing party would be represented by the IT firms that actually handle the technical functions through which user data is processed.
The GDPR will affect all controllers and processors that handle the personal data of EU residents, regardless of whether the controlling or processing parties in question are based in Europe or abroad. As such, the new law affects all online businesses and platforms that accept international customers or members.
Regarding GDPR fulfillment, the balancing act between controllers and processors works as follows — the controllers must ensure that their processors function in accordance with the new regulations, while the processors themselves must make sure that their activities abide the new law and maintain applicable records.
If the latter party holds full or even partial responsibility for a data breach, the processor will be penalized much more strictly under the incoming regulations than under the pre-existing Data Protection Act. The actual source of a breach won't even matter under the new law, as the processor will bear most of the blame.
How Is Data Processed Under the GDPR?
As soon as the GDPR is implemented on May 25, 2018, controllers will be required under law to process EU user data for specific purposes with complete transparency. Once the purpose is completed, and the controlling/processing entities have no lawful need for the data of a given user, the data must be deleted. Therefore, personal data will no longer be stored idly and indefinitely on servers that could be hacked at any time.
What Does the Word "Lawful" Entail Under the GDPR?
The word "lawful" covers a spectrum of meaning within the parlance of GDPR application. On the one hand, the use of private data could be considered lawful if the person in question has consented to the use of his or her personal information. Alternately, "lawful" could apply to the following four justifications:
-
compliance with a legal contract
-
the protection of an interest deemed essential to the life of an individual
-
the processing of data within the interest of the public
-
the prevention of fraud
 For the personal data of EU residents to be processed lawfully under the GDPR, at least one of the justifications mentioned above will have to apply. The law is designed to put the interests of online users above the entities that could be intent on exploiting or sharing personal data.
For the personal data of EU residents to be processed lawfully under the GDPR, at least one of the justifications mentioned above will have to apply. The law is designed to put the interests of online users above the entities that could be intent on exploiting or sharing personal data.
How Is Consent Granted Under the GDPR?
For controllers to get the agreement of an individual, the person must give consent through a direct, confirmed action. The pre–existing standard of justification, which allows controllers to use data with only passive acceptance on the part of the person, will not suffice under the GDPR. Therefore, consent cannot be gained through means that would only be understood by users who parse the fine print of a given set of terms.
For example, an interface that obtains consent in a manner that could be confusing to a customer — or that automatically renews a customer without consent unless the customer in question follows a set of complex steps to explicitly withdrawal — will not be allowed under the GDPR.


It's the controller's obligation to keep a record of the time, date and means through which a person has given his or her consent, and to respect the individual's wish to withdrawal at any time. Any business, charity or government agency that doesn't currently conform to these new regulations will have to bring their protocols into compliance by the date at which the GDPR takes effect. For many companies, the implementation of best–practice standards has made this transition a whole lot easier.
What Is Considered Private Data Under the GDPR?
The category that constitutes private data within the EU has become a whole lot broader under the GDPR. In response to the type of information that companies now gather from individuals, information about a user's computer and location, as indicated by an IP address, will now be considered private data. Other information, such as the financial, psychological or ethnic history of an individual, would also be defined as personal information. Anything that could be used to identify an individual would qualify.
Additionally, anonymized information about an individual could also be defined as private data, as long as the information in question could easily be traced back to the real identity of the person in question. If a person has lived under an alias or pseudonym, yet the duo identity is widely known, that would be considered personal information. Of course, anything already defined as private under the Data Protection Act will also fall under the definition of personal information/private data under the GDPR.
When Can an Individual Access His or Her Stored Private Data?


A person can request to see his or her private data at reasonable intervals, as defined by the GDPR. Under the new law, controllers will be obligated to respond to a user's request within 30 days. The new regulations will also require controllers and processors to maintain policies of transparency regarding the means through which data is gathered, used and processed. The language used to explain these processes to people must be worded in simple, clear layman's terms and not be littered with confusing jargon. It can't read like a formal, legal document.
Each individual is entitled to access any private data held by a company. Furthermore, each individual has the right to know just how long his or her information will be stored, which parties will get to view it and the reasons for which the data is being used. Whenever possible, controllers will be encouraged to offer secure viewing access for any account holder who wishes to see his or her personal information, as held in a company's database. People will also be able to request that incorrect or incomplete data be corrected at any time.
What Is the "Right to be Forgotten"?

A person can request that his or her data be deleted at any time, for any reason, under a clause of the GDPR known as the "right to be forgotten." If an individual feels that his or her data is no longer essential for the original purpose of its collection — such as when an address is collected to verify that a person meets the geographical requirements for participation in a contest or survey — a request can be made to have the information removed from a database.
In keeping with this principle, a person can also request that his or her data be deleted from a server if the individual withdraws consent for the data collection, or if the individual directly opposes the way that the data has been processed. When a request to be forgotten has been made, the controller is obligated to inform Google and other data–gathering organizations that all copies and links to said data must be deleted. The risk of having dormant personal info leaked to third–party marketers will be greatly minimized under the new law.
What If a Person Wants to Transfer His or Her Data Elsewhere?
Under the GDPR, EU residents will be able to request that information be moved from one database to another, free of charge, for any reason. The law stipulates that controllers will be required to store private data in formats of common use, such as CSV, that make it easy to transfer data from one organization to another. All such requests for personal data transfer must be honored within 30 days. The process for making such requests will also be simplified under the new law.
What If an Organization Is Hit With a Data Breach?

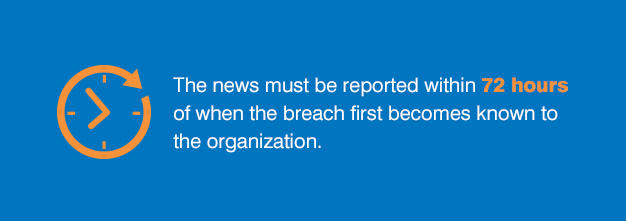
Any organization that collects the private data of users is required to report news of a data breach to a protection authority. The news must be reported within 72 hours of when the breach first becomes known to the organization. In the United Kingdom, the Information Commissioner's Office (ICO) serves as the authority on such matters. Once the GDPR goes into effect, the UK is expected to expand oversight on such issues.
The 72–hour deadline to report a breach will not always give an organization enough time to learn the full nature of a particular offense, but it should provide sufficient time to gather adequate information for the authority about the kind of data that will be affected by said breach. Just as importantly, an organization should be able to give a rough estimate of the number of people that will be impacted by the breach. This way, potentially affected parties will have more time to react.


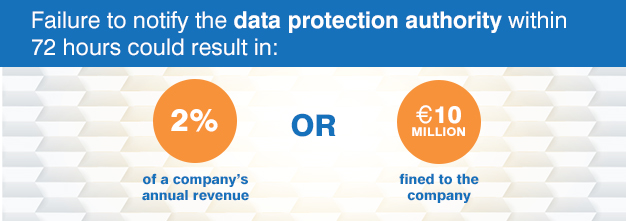
Before a call is even placed to the data protection authority, the people who could be affected by the breach should be notified. Failure to notify the data protection authority within 72 hours could result in a fine of as much as 2% of a company's global annual revenue, or a fine of €10 million — whichever happens to be the larger amount. Compared to current ICO fines, which only go as high as £500,000, the penalties under the GDPR are far stricter.

What Additional Non–compliance Fines Do Organizations Face Under the GDPR?
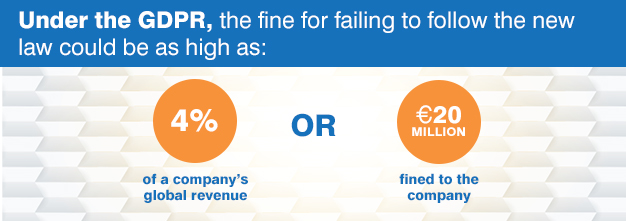
If an organization fails to abide by the core principles of the GDPR — such as gaining the consent, respecting the rights, and obeying the requests of individuals — the organization could face fines twice as high as those imposed for failure to report a data breach. Under the GDPR, the fine for failing to follow the new law could be as high as 4% of a company's global revenue, or a fine of €20 million — whichever happens to be the larger amount.

How Will the GDPR Impact The UK After Brexit?
Until the UK actually withdraws from the EU, companies based in England, Scotland and Wales will still have to be in full compliance with the new laws. British citizens, meanwhile, will be protected under the GDPR until Brexit takes effect. Once the UK has completed its exit from the EU, British companies will still be required to follow the new regulations when handling the private data of EU citizens.
Because the GDPR will go into law before Brexit takes place, any new data–protection legislation that the UK implements will likely be designed to work in compliance with EU regulations, rather than force the EU to accommodate UK standards. As such, there won't likely be much difference between the GDPR and British laws on information protection in the foreseeable future, if ever.
How Will the GDPR Affect Smaller Businesses?
Compliance with the GDPR could be complicated at first for companies that haven't even begun the process of updating systems to meet the new regulations. This holds especially true for smaller businesses, which might lack the infrastructure to complete such changes before the law takes effect on May 25, 2018.
For small companies that are just beginning — or have yet to prepare — for implementation of the GDPR, it will likely be best to hire a third–party entity, such as a security or consultancy firm, to help with the process of bringing systems into full compliance. Better yet, the adoption of best–practices standards can contribute to ensuring that compliance is largely met in advance of any audits or assessments.
One of the clearest–cut consequences for organizations that fail to comply with the new regulations are the penalties that follow a security breach. The party responsible for a data breach — be it an outside hacker, an inside rogue or an unidentified source — won't matter under the GDPR, which places full responsibility on the organization itself. For small businesses in particular, these policies and the resulting fines will make compliance especially important. To that end, the early adoption of best–practices standards can save smaller businesses a whole lot of money.
What Benefits Do Companies Gain Under the GDPR?
When a company's database is brought into compliance with the GDPR, the benefits are multifaceted. For starters, the regulations can help a company establish better practices for the handling and security of collected information. After all, when customers or site members reap benefits, the businesses and platforms in question earn better reputations, which lead to more sales and sign ups.
Compliance can also ensure that a company adopts protocols that keep processes updated in a timely manner. Furthermore, the GDPR will likely motivate companies to improve the integrity of collected data. Over time, companies may even be inspired to develop better methods for capturing and storing leads and customer information.
How Will the Changes Affect Businesses That Are Already Regulated?
Organizations that are already regulated under best–practice models like the FCA or PRA will probably see few changes under the GDPR. Likewise, if a business is accredited with ISO 27001 certification, few changes are likely to be necessary once the EU regulations take effect.
For companies that lack these models or certifications and have yet to adapt to newer, higher standards of security, the future law will be a lot harder to come into compliance with by May 25, 2018. The sooner a company begins the preparation process, the easier and less risky or costly it will be to collect and handle private data once the regulations are implemented. This is one of the primary reasons why more companies across the globe are implementing ISO 27001 as a best–practices standard.
How Can ISO 27001 Help With GDPR Compliance?


Organizations around the world that have studied the GDPR are likely aware that the regulations are an encouragement to adopt best–practice schemes. As businesses and government agencies prepare for the implementation of the EU law, new systems are being developed to further enhance best–practice models in the areas of data security.
ISO 27001 is an information security standard that helps companies come into compliance with international best–practice models. The standard covers three key components of data security — people, processes and technology. When steps are taken to safeguard data with these three components in mind, businesses are better equipped to protect information, mitigate risks and rectify procedures that are deemed ineffective. As such, a growing consensus has emerged in the corporate sector that deems ISO 27001 to be the gold standard in best–practice schemes.
By putting the ISO 27001 standard into effect, an organization activates an information security management system (ISMS) that works within the business culture of the company in question. The standard is regularly updated and enhanced, and these ongoing improvements allow the ISMS to stay abreast of changes both within and outside of the company, all the while spotting and eliminating new risks.
How Does ISO 27001 Apply to Articles in the GDPR?
In Article 32 of the GDPR, policies are outlined for the encryption of data, the assurance of confidentiality and availability and the testing of security. So how does ISO 27001 work the incoming EU law? In the following ways:
Data encryption. This is encouraged by ISO 27001 as the primary method to reduce the possibility of risks. In ISO 27001:2013, more than one hundred controls are outlined for use, each of which can be implemented to lower the possibility of security risks. With each control based on the result of a previous risk assessment, any organization that utilizes the standard can pinpoint the at–risk assets and apply the necessary encryption.
Confidentiality, integrity and availability of data. This is one of the fundamental principles of ISO 27001. While the confidentiality of data is the bedrock of customer trust in an online company, the integrity and availability of private information is also crucial. If the data can easily be accessed, but the format is unreadable due to system errors, the data has lost its integrity. By the same token, if the data is safe yet out of reach to a person who needs it, the data can't be considered available.
Risk assessment. According to ISO 27001, an organization must enact complete evaluations of all possible vulnerabilities that could impact a company's data, and to leave no stone unturned in the effort to safeguard the privacy, accessibility and integrity of that information. At the same time, the standard discourages the use of overbearing security protocols that could hinder a company's ability to operate efficiently.
Business continuity. In ISO 27001, the fundamentals of continuity in business management are laid out, whereby controls are implemented to help a company keep vital information readily available in the event of a system interruption. These same protocols can assist a business in its quick recovery from what would otherwise be a lengthy and costly shutdown. With the standard in place, companies experience little, if any, downtime.
Testing and assessments. An organization that gains ISO 27001 certification receives assessments and audits of its ISM by a third–party certification firm. This ensures that the ISM is compliant with the standard. Any company that implements the standard must keep its ISM under constant review to ensure that it remains protective of private data.
Compliance. According to control A.18.1.1 of ISO 27001 — which concerns the identification of applicable legislation and contractual requirements — an organization must list all legislative, regulatory and contractual requirements. If an organization is required to comply with the GDPR, this must be listed as one of the regulatory requirements. Even without the EU law, control A.18.1.4 leads organizations that utilize the standard through the process of enacting data protection.
Breach notification. ISO 27001 control A.16.1 ensures the efficient management of security incidents, which helps organizations come into compliance with the GDPR, under which authorities must be notified within 72 hours of the discovery of a data breach. Companies that have implemented the standard are faster to respond to such incidents, which makes compliance in this area easier to meet.
Asset management. This is addressed under ISO 27001 control A.8, which includes personal data as an information security asset. Organizations that implement the standard are given an understanding of which types of data are essential, as well as where such data must be stored and for how long. Control A.8 also covers the origin of personal data and the party that gets to access said data, all of which are requirements of GDPR.
Of course, the requirements of ISO 20071 extend far beyond the principles as mentioned earlier. As an all–encompassing best–practices standard, various other areas are also covered, such as methods that apply to staff training. The standard has been implemented by countless organizations throughout the world. With the frequency and consequences of today's data breaches, the standard has become an essential part of data security in the digital marketplace.
Is ISO 27001 Enough for GDPR Compliance?
While there are some areas covered under the GDPR that are not controlled under the ISO 27001 standard — such as the right of a data subject to have his or her data moved or deleted — the standard covers most of the requirements of the new law by virtue of the fact that private data is recognized as an information security asset under ISO 27001. As such, the standard and the new regulations share like–minded views on data security.
Essentially, any company that interacts with EU residents will need to reach compliance with the GDPR. Because ISO 27001 is considered far and wide as the most secure of all the best–practice standards, it will likely prove to be the most applicable standard under the new regulations. Already, more and more companies are swiftly implementing the standard in advance of the new law.
How Can an ISO 27001–certified Company Ensure That It's Also GDPR Compliant?
ISO 27001 is one of the most applicable standards for GDPR compliance. If the standard has already been implemented by a company, said company is already more than half prepared for the incoming EU regulations. To verify whether full compliance has been reached, any concerned company should run a GDPR GAP analysis, which will pinpoint any requirements that still need to be added to the ISM of an already implemented ISO 27001.


How Will the GDPR Affect Companies Based in the US?
Any company in the US that profiles of sells products to EU residents will need to bring its data system into compliance with the GDPR by May 25, 2018. Granted, while many stateside companies already have privacy policies in place that are designed to meet compliance with pre–existing EU laws, revisions will need to be made by these companies in preparation for the upcoming regulations. Any company that has thus far relied on pre–cloud security standards will need to bring its systems up to speed and fast.
How Will the GDPR Impact Companies Around the Globe?
No matter where in the world a company is based outside the EU, that company will still need to be in compliance with the GDPR as long as it gathers the personal data or sells goods or services to EU residents. This would apply to any company worldwide that collects money or information from people on the Internet.
The penalties for non–EU companies that fail to meet GDPR compliance will be the same as for European–based companies. Therefore, failure to follow the incoming EU regulations could result in whichever of the following fines constitutes the greater amount — a fine that equals €20 million, or a fine that takes 4% of a company's annual revenue. These penalties will apply to companies in nations across the globe — Canada, Japan, Brazil, China, Australia, India, South Africa, Argentina — as long as said companies do business with the residents of any EU nation.
At NQA, we help companies bring systems into compliance with the current standards of the digital environment. To learn more about how we can help you prepare for the GDPR, contact us today to request a quote.
Reviewed by: Tim Pinnell, NQA Information Security Assurance Manager 12/18/2020
